CRITICAL INTERFACE TOOLBOX
[AN ONLINE RESOURCE FOR CRITICAL INTERFACE DESIGN]
THE CRITICAL INTERFACE TOOLBOX unfolds as an online resource that exposes experimental methodologies, practices, and tools aimed at enhancing critical thought towards the actual configuration of the Interface. These actions were developed within a year-long research project at HANGAR. This initiative is part of the European Consortium IMAGIT and fits in with the research and actions developed at the Interface Manifesto.
[1] The interface is a device designed and used to facilitate the relationship between systems.
[2] (To) interface is a verb (I interface, you interface ...). The interface occurs, is action.
[3] The interface exists in the crease between space and time; it is a device and simultaneously a situation. It is rendered (updated under thoughtful conditions) and emergent (joining into something new).
[3] The interface collects traces: traces and remains of all agents/agencies which converge in it.
[4] The interface is the tip of the iceberg of a complex system of agents/agencies, of interdependent infrastructures, codes, data, applications, laws, corporations, individuals, sounds, spaces, behaviors, objects, protocols, buttons, times, affects, effects, defects ...
[5] An interface is designed within a cultural context and in turn designs cultural contexts.
[6] The interface responds and embodies the economic logic of the system in which you enroll. It is a political device.
[7] The ideology of the interface is always embedded in the interface itself, but it is not always visible.
[8] Can we make the invisible visible? The more present interfaces are in our lives, the less we perceive them.
[9] The interface uses metaphors that create illusions: I am free, I can go back, I have unlimited memory, I am anonymous, I am popular, I am creative, it's free, it's neutral, it is simple, it is universal. Beware of illusions!
[10] The standard calls for a universal subject and generates processes of homogenization, but reduces the complexity and diversity . What is not standard?
[11] Users are entitled to know what the interface hides. Access to knowledge is a fundamental right.
[12] In the design of the interface, not only skills but also emotions and affections are deployed. How are emotions produced and circulated in interfaces?
[13] The user uses the interface perform agency, they coproduce each other and therefore they have the ability to define, redefine and contradict themselve by action or omission.
B-FACE, 2016. Diego Paonesa.
Touching Software, 2016. Ben Grosser.
Defooooooooooooooooooooorest, 2016. Joana Moll.
Google & Friends, 2015. The Institute for the Advancement of Popular Automatisms.
Dance for mobile phones, 2015. Evan Roth.
CO2GLE, 2015. Joana Moll.
Body Interfaces, 2015. Tina Madsen.
Interfight, 2015. César Escudero Andaluz.
Anxious to Make, 2015. Liat Berdugo & Emily Martinez
Facebook mood modificator, 2014. Lauren McCarthy.
Tapebook, 2014. César Escudero Andaluz.
Google Image Quiz, 2014. Silvio Lorusso.
Vincent's Facebook, 2013. Cubanradio.
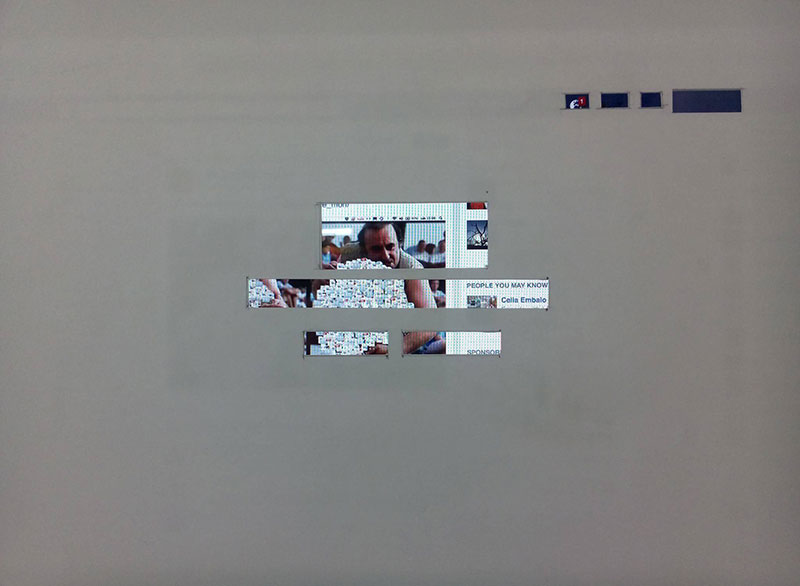
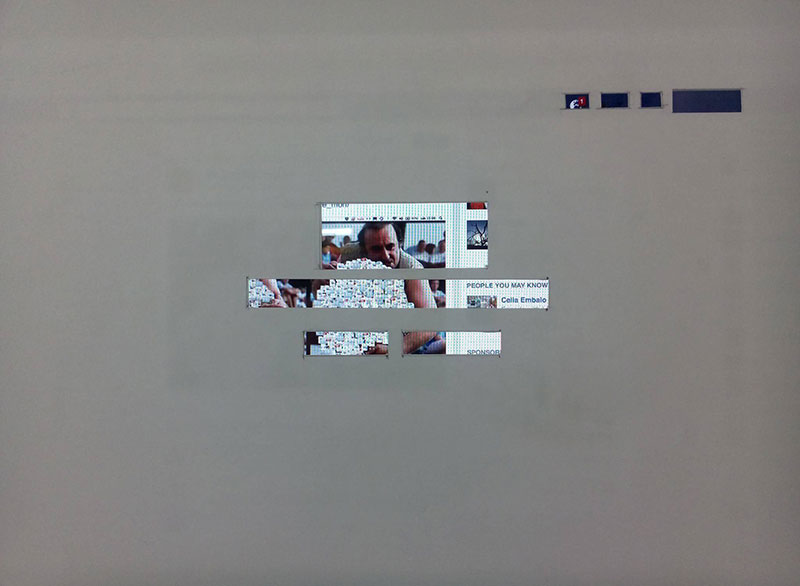
Dark side of the Prism, 2013. Justin Blinder.
Portrait of a web server, 2013. Jan Robert Leegte.
The Bible as a hyperlink, 2013. Jan Robert Leegte.
Mouse Pointer, 2013. Jonas Lund.
Level Cleared, 2012. Evan Roth.
File Món, 2012. César Escudero Andaluz.
Facebook Demetricator, 2012. Ben Grosser.
Untitled Internet, 2012. Constant Dullaart.
Reload the Love, 2011. Ben Grosser.
Newstweek, 2011. Julian Oliver.
Facebook Bliss, 2010. Anthony Antonellis.
Google Variations, 2010. Leonardo Solaas.
Net Sonification, 2008. Zach Layton.
The Internet Overexposed, 2008. Jan Robert Leegte.
Jodi, 1999 - 2016. Jodi.
BROWSER PLUGINS
NO SCRIPT
Allows executable web content such as JavaScript, Java, Flash, Silverlight, and other plugins only if the site hosting is considered trusted by its user and has been previously added to a whitelist
PRIVACY BADGER
Blocks advertisements and tracking cookies that do not respect the Do Not Track setting in a user's web browser
DISCONNECT
Visualizes and blocks invisible sites that track your search and browsing history
GHOSTERY
Enables its users to easily detect and control javascript code that are embedded in a web page, invisible to the user - freeware but proprietary code
REQUEST POLICY
Increases your browsing privacy, security, and speed by giving you control over cross-site requests
WHAT FACEBOOK THINKS YOU KNOW
Allows you to navigate how FaceBook collects your data
FACEBOOK TRACKING EXPOSED
Acts as a third party in your service: it is able to measure how much these algorithms are not neutral
MOBILE APPS
FDROID
A software repository for Android applications, similar to the Google Play store, containing only apps which are free software
AFWALL+
An advanced iptables firewall editor for Android. It provides fine-grained control over which Android apps are allowed to access the network
CSIPSIMPLE
A Voice over Internet Protocol application for Android operating system using the Session Initiation Protocol, with support for ZRTP encryption
ORBOT
A free software project to provide anonymity on the Internet for users of the Android operating system. It acts as an instance of the Tor network
ORFOX
A Tor Browser for Android, with a few minor modifications to the privacy enhancing features to make them compatible with Firefox for Android
SIGNAL
Free, worldwide, encrypted voice calls for iPhone, and fully compatible with RedPhone for Android - Proprietary code used for voice calls
CHAT SECURE
A free and open source messaging app that features OTR encryption over XMPP (Jabber)
CYANOGENMOD
An open-source operating system for smartphones and tablet computers, based on the Android mobile platform
DATA TRANSPARENCY
IPHONE TRACKER
Maps the information that your iPhone is recording about your movements
COOKIEPEDIA
Provides detailed information all about cookies, the types of data they collect, and the websites that use them.
FLOODWATCH
A Chrome extension that tracks the ads you see as you browse the internet
TERMS OF SERVICE
A project started in 2012 to help fix the “biggest lie on the web”: almost no one really reads the terms of service we agree to all the time
PANOPTICLICK
Analyzes how well your browser and add-ons protect you against online tracking techniques, checks if your system is uniquely configured, and thus identifiable, even if you are using privacy-protective software
BROWSERS
TOR BROWSER
A modified Firefox ESR, pre-configured to protect users' privacy and anonymity on the web, bundled with Tor to allow users to use the Tor anonymity network
ENCRYPTION
TAILS
A live operating system, that you can start on almost any computer from a DVD, USB stick, or SD card, which aims at preserving your privacy and anonymity
GPG
A complete and free implementation of the OpenPGP standard, which allows to encrypt and sign your data and communication
LUKS
Linux Unified Key Setup or LUKS is a disk encryption specification, which specifies a platform-independent standard on-disk format for use in various tools
VERACRYPT
An open-source freeware utility used for on-the-fly encryption. It can create a virtual encrypted disk within a file or encrypt a partition or the entire storage device with pre-boot authentication
ONIONSHARE
An open source tool that lets you securely and anonymously share a file of any size
OTR CHAT
Off-the-Record (OTR) Messaging allows you to have private conversations over instant messaging
POSTEO MAIL
An email provider based in Berlin with a strong focus on sustainability and security
PROTONMAIL
An encrypted-email service which uses client-side encryption to protect email contents and user data before they are sent to ProtonMail servers
DATA VISUALIZATION
OPEN VISUAL TRACEROUTE
An pen source cross-platform Java Visual Traceroute, packet sniffer and Whois. Data is displayed in a 3D or a 2D map component
LIGHTBEAM
Enables you to see the first and third party sites you interact with on the Web, using interactive visualizations, and shows you the relationships between these third parties and the sites you visit
NMAP
A security scanner used to discover hosts and services on a computer network, thus creating a "map" of the network
WIRESHARK
A free and open source packet analyzer, used for network troubleshooting, analysis, software and communications protocol development, and education
OTHERS
JUST DELETE ME
A website and browser extension which helps you delete your accounts from many web services
FAKE IDENTITY GENERATOR
Generates a fake name, address, date of birth, username, password and biography
RUIN MY SEARCH HISTORY
Ruins your Google search history with a single click
GUERRILLA MAIL
Disposable Temporary E-Mail Address
ELECTRONIC FRONTIER FOUNDATION
RISEUP
AUSTISTICI
TACTICAL TECH COLLECTIVE
SERVUS.AT
DATA UNION
INSTITUTE OF NETWORK CULTURES
DISRUPTION NETWORK LAB
NETWORKED LABOUR
SHARE LAB
SHARE FOUNDATION
ANNE HELMOND
DYNAMICS OF VIRTUAL WORK
DYNE.ORG
GLOBAL GUERRILLAS
SHARE FOUNDATION
DATA ACTIVE
BITS OF FREEDOM
SECURITY IN A BOX
MY SHADOW
EXPOSING THE INVISIBLE
FACEBOOK ALGORITHMIC FACTORY
METADATA INVESTIGATION: INSIDE HACKING TEAM
ANNE HELMOND
INSITUTE FOR THE ADVANCEMENT OF POPULAR AUTOMATISMS
DISNOVATION
CITIZEN EX
DATA DEALER
COMMODIFY US
RUIN MY SEARCH HISTORY
HOW MUCH IS YOUR DATA WORTH?
CRITICAL ATLAS OF INTERNET
MAP OF THE INTERNET
Shoshana Zuboff (March 5, 2016). The Secrets of Surveillance Capitalism. Feuilleton. Retrieved from http://www.faz.net/aktuell/feuilleton/debatten/the-digital-debate/shoshana-zuboff-secrets-of-surveillance-capitalism-14103616.html
John Naughton (2015, December 6). ALGORITHM WRITERS NEED A CODE OF CONDUCT. The Guardian. Retrieved from http://bit.ly/2cknps6
Adam D. I. Kramera, Jamie E. Guilloryb, and Jeffrey T. Hancockb, (March 25, 2014). FEXPERIMENTAL EVIDENCE OF MASSIVE-SCALE EMOTIONAL CONTAGION THROUGH SOCIAL NETWORKS. Princeton University. Retrieved from http://www.pnas.org/content/111/24/8788.full
Zoe Corbyn (12 September, 2012). FACEBOOK EXPERIMENTS ON VOTER. University of California, Berkeley - School of Law. Retrieved from http://www.nature.com/news/facebook-experiment-boosts-us-voter-turnout-1.11401
Evgeny Morozov (October 22, 2013). THE REAL PRIVACY PROBLEM. MIT Technology Review. Retrieved from https://www.technologyreview.com/s/520426/the-real-privacy-problem/
Meghan O’Gieblyn (February 09, 2016). As a God Might Be, Three Visions of Technological Progress. Boston Review. Retrieved from https://bostonreview.net/books-ideas/meghan-ogieblyn-god-might-be?utm_content=buffer4e2b3&utm_medium=social&utm_source=twitter.com&utm_campaign=buffer
Lídia Pereira (January 22, 2016). Corporate Social Networking Platforms As Cognitive Factories. Institute of Network Cultures. Retrieved from http://networkcultures.org/longform/2016/01/22/corporate-social-networking-platforms-as-cognitive-factories/
Pamela Samuelson (May 11, 2015). FREEDOM TO TINKER. University of California, Berkeley - School of Law. Retrieved from http://papers.ssrn.com/sol3/papers.cfm?abstract_id=2605195
Neil Lawrence (March 5, 2015 ). Beware the rise of the digital oligarchy . The Guardian. Retrieved from https://www.theguardian.com/media-network/2015/mar/05/digital-oligarchy-algorithms-personal-data
Joanna Geary (April 23, 2012 ). Tracking the trackers: What are cookies? An introduction to web tracking . The Guardian. Retrieved from https://www.theguardian.com/technology/2012/apr/23/cookies-and-web-tracking-intro
Doc Searls (June 7, 2016). What's Our Next Fight? Linux Journal. Retrieved from https://www.linuxjournal.com/content/whats-our-next-fight
Bob Dormon (May 24, 2016). How the Internet works: Submarine fibre, brains in jars, and coaxial cables. Ars Technica. Retrieved from http://arstechnica.co.uk/information-technology/2016/05/how-the-internet-works-submarine-cables-data-centres-last-mile/
Andersen, C.U. y Pold, S., 2011. Interface criticism aesthetics beyond buttons. Aarhus [Denmark]; Oakville, CT: Aarhus University Press ; David Brown Book Co. ISBN 87-7124-239-2.
Barry, A., Arti ce and Design: Art and Technology in Human Experience, Cornell University Press, 2008.
Benjamin, W., La obra de arte en la era de su reproducibilidad técnica, Godot, Barcelona, 2012. Berardi, F., La sublevación, Surplus, Oaxaca, 2014.
Bertelsen, O.W. y Pold, S., 2004. Criticism as an approach to interface aesthetics. Proceedings of the third Nordic conference on Human-computer interaction. ACM Press, pp. 23–32.
Castells, M., La Sociedad Red, Alianza Editorial, Madrid, 2006. Cox, G., Mc Lean, A., Speaking Code, MIT Press, Boston, 2012.
Deleuze, G., Guattari, F., A ousand Plateaus: Capitalism and Schizophrenia, A&C Black, London, 2004.
Feenberg, A., Transformar la Tecnología, Universidad Nacional de Quilmes, Buenos Aires, 2012. Foucault, M., e Archaeology of Knowledge, Paperback, London, 1982.
Fuller, B., Utopia or Oblivion: e Prospects for Humanity, Bantam Books, Nueva York, 1969. Fuller, M. (ed.), 2008. Software studies: A lexicon. Cambridge, Mass.: MIT Press. [Accessed: 26 abril 2016]. ISBN 978-0-262-27334-3.
Fuller, M. y Go ey, A., 2012. Evil Media. Cambridge, Mass: e MIT Press. ISBN 978-0-262-01785-5.
Galloway, A.R., 2012. e interface e ect. Cambridge, UK; Malden, MA: Polity. ISBN 978-0-7456-6252-7.
Grosser, B., 2014. What Do Metrics Want? How Quanti cation Prescribes Social Interaction on Facebook. Computational Culture: a journal of software studies [online], Available at: http://computationalculture.net/article/what-do-metrics-want.
Harrel, F., Phantom Media, MIT Press, Boston, 2014.
Illich, I., La Convivencialidad, Fondo de Cultura Económica, México DF, 2006.
Latour, B., 2005. Reassembling the Social: An Introduction to Actor-Network eory. S.l.: Oxford University Press, USA.
Latour, B., Nunca Fuimos Modernos, Siglo 21 Editores, México DF, 2007.
Liliana, O., 2012. Turing Complete User [en línea]. octubre 2012. [Retrieved: 1 junio 2016]. Available at: http://contemporary-home-computing.org/turing-complete-user/.
Manovich, L., 2002. e Language of New Media. Reprint edition. Cambridge, Mass.: e MIT Press. ISBN 978-0-262-63255-3.
Manovich, L., 2013. Software Takes Command. New York: Continuum Publishing Corporation. ISBN 978-1-62356-745-3.
Marcuse, H., El hombre unidimensional, Ariel, Madrid, 2010. Morozov, E., To Save Everything Click Here:, Paperback, London, 2013.
Padilla, M., 2014. Las interfaces: tres instantáneas [en línea]. 10 junio 2014. Retrieved from: http://pipes.hangar.org/wp-content/uploads/2014/06/interfaces_para_publi- car_margarita_padilla.pdf.
Parikka, J., A Geology of Media, University of Minnesota Press, Minnesota, 2015.
Penny, S., Badia, T., Garcia, M., Parés, R., Balestrini, M., Seebach, S., Perelló, J., et alt., 2015. Protocol para la Investigación Interdisciplinar. [en línea]. [Accessed: 3 junio 2016]. Retrieved from: https://wirkt.hangar.org/index.php/Main_Page.
Shirky, C., Cognitive Surplus, e Penguin Press, New York, 2010.
Terranova, T., Free Labour, Producing Culture for the Digital Economy, London, 2003. Tiqqun, La Hipótesis Cibernética, Acuarela & A. Machado, Madrid, 2015.
Wark, M., Un Manifesto Hacker, Alpha Decay, Barcelona, 2006.
Wiener, N., Cibernética, Barcelona, Tusquets, Barcelona,1985.
RESEARCH
JOANA MOLL
ANDREA NONI
MANAGEMENT & COORDINATION
TERE BADIA
CLARA PIAZUELO
MARTA GRACIA
HANGAR
EUROPEAN CONSORTIUM IMAGIT
Karlsruhe University of Arts and Design – HfG (Karlsruhe, Germany) coordinator of the project.
HANGAR (Barcelona).
Hungarian University of Fine Arts – HUFA (Budapest, Hungary).
Brainz (Prague, Txec Republic).


MAIN RESEARCH TOPICS
#Internet Physicality; #Geopolitics of the Internet; #Internet Backbone; #Data Flows & CO2 emissions; #Online Tracking; #Data Privacy; #Code; #Language; #Cognitive Capitalism; #Anthropocene; #Algorithmic Politics; #Social Engineering; #Interface Governance; #Critical Design; #Quantification; #Corporate Design; #Community Design; #Hacktivism.
CONTENTS
[1]RESEARCH CRITICAL INTERFACE MANIFESTO
[2]RESEARCH A POETIC DECONSTRUCTION OF THE INTERFACE
[3]RESEARCH TRACKING FORENSICS
[4]RESOURCES ARTISTIC APPROACHES TO THE INTERFACE
[5]RESOURCES TOOLS
[6]RESOURCES RESEARCH & NETWORK ACTIVISM
[7]RESOURCES PROJECTS
[8]RESOURCES TEXTS
[9] ABOUT
[2]RESEARCH A POETIC DECONSTRUCTION OF THE INTERFACE
[3]RESEARCH TRACKING FORENSICS
[4]RESOURCES ARTISTIC APPROACHES TO THE INTERFACE
[5]RESOURCES TOOLS
[6]RESOURCES RESEARCH & NETWORK ACTIVISM
[7]RESOURCES PROJECTS
[8]RESOURCES TEXTS
[9] ABOUT
This workshop sought to critically reveal, analyze and connect the complex network of agents that converge on the configuration of the Interface. During a 3 weekend-long workshop we revealed, deconstructed and re-articulated the material and immaterial elements that construct the Interface in order to reflect on its role and influence within the social, political, economic, cultural and emotional spheres of the networked society. Therefore, the main goal of the workshop was to stimulate and re-appropriate subjectivity, an essential process in the generation of critical thought about the true nature of technology, and in the imagination of alternative techno-paradigms which may coherently respond to our environmental and human conditions.
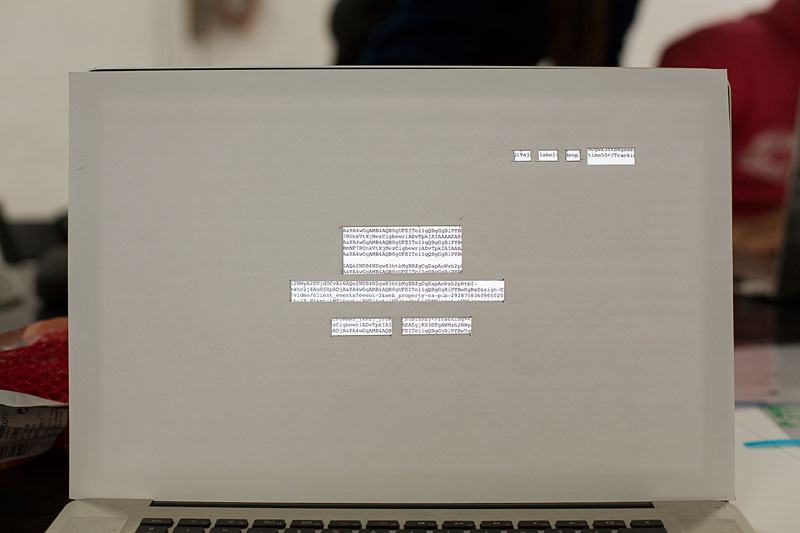
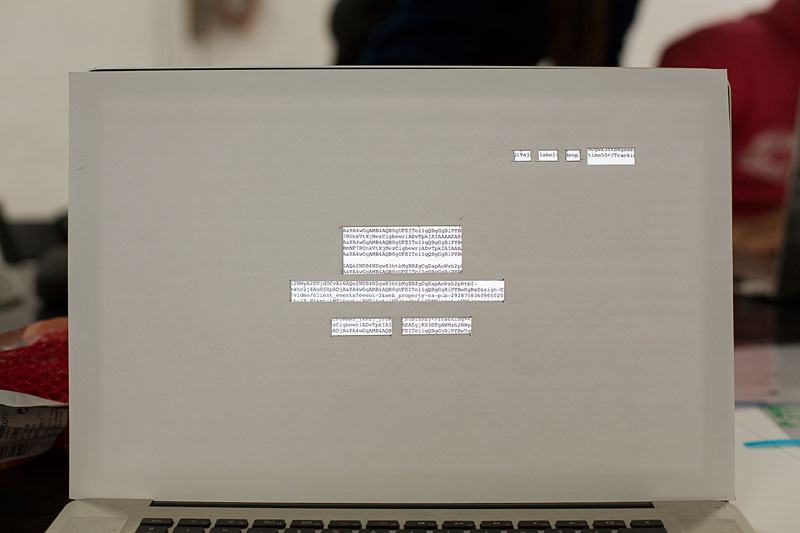
Far from being a purely immaterial entity, the Internet is an extremely complex physical structure composed by a massive number of actors that have a direct and deep impact in every aspect of our daily lives. Despite its crucial role in many aspects of our society, the material and computational architectures that allow the Internet to exist are widely ignored by most of its users. Thus, this workshop seeks to critically reveal and analyze the complex network of agents that come together to configure the Internet, from submarine and underground cables to geopolitics, online tracking, surveillance and privacy. The workshop will strongly focus on uncovering and analyzing common online tracking practices used by major marketing and advertising corporations. To achieve this purpose, we will look into the forensics of the physical pathways of information, and will apply reverse tracking methods aimed at drawing a map of the many corporations that covertly access and commodify our data.


[4] ARTISTIC APPROACHES TO THE INTERFACE
B-FACE, 2016. Diego Paonesa.
Touching Software, 2016. Ben Grosser.
Defooooooooooooooooooooorest, 2016. Joana Moll.
Google & Friends, 2015. The Institute for the Advancement of Popular Automatisms.
Dance for mobile phones, 2015. Evan Roth.
CO2GLE, 2015. Joana Moll.
Body Interfaces, 2015. Tina Madsen.
Interfight, 2015. César Escudero Andaluz.
Anxious to Make, 2015. Liat Berdugo & Emily Martinez
Facebook mood modificator, 2014. Lauren McCarthy.
Tapebook, 2014. César Escudero Andaluz.
Google Image Quiz, 2014. Silvio Lorusso.
Vincent's Facebook, 2013. Cubanradio.
Dark side of the Prism, 2013. Justin Blinder.
Portrait of a web server, 2013. Jan Robert Leegte.
The Bible as a hyperlink, 2013. Jan Robert Leegte.
Mouse Pointer, 2013. Jonas Lund.
Level Cleared, 2012. Evan Roth.
File Món, 2012. César Escudero Andaluz.
Facebook Demetricator, 2012. Ben Grosser.
Untitled Internet, 2012. Constant Dullaart.
Reload the Love, 2011. Ben Grosser.
Newstweek, 2011. Julian Oliver.
Facebook Bliss, 2010. Anthony Antonellis.
Google Variations, 2010. Leonardo Solaas.
Net Sonification, 2008. Zach Layton.
The Internet Overexposed, 2008. Jan Robert Leegte.
Jodi, 1999 - 2016. Jodi.
[5] TOOLS
BROWSER PLUGINS
NO SCRIPT
Allows executable web content such as JavaScript, Java, Flash, Silverlight, and other plugins only if the site hosting is considered trusted by its user and has been previously added to a whitelist
PRIVACY BADGER
Blocks advertisements and tracking cookies that do not respect the Do Not Track setting in a user's web browser
DISCONNECT
Visualizes and blocks invisible sites that track your search and browsing history
GHOSTERY
Enables its users to easily detect and control javascript code that are embedded in a web page, invisible to the user - freeware but proprietary code
REQUEST POLICY
Increases your browsing privacy, security, and speed by giving you control over cross-site requests
WHAT FACEBOOK THINKS YOU KNOW
Allows you to navigate how FaceBook collects your data
FACEBOOK TRACKING EXPOSED
Acts as a third party in your service: it is able to measure how much these algorithms are not neutral
MOBILE APPS
FDROID
A software repository for Android applications, similar to the Google Play store, containing only apps which are free software
AFWALL+
An advanced iptables firewall editor for Android. It provides fine-grained control over which Android apps are allowed to access the network
CSIPSIMPLE
A Voice over Internet Protocol application for Android operating system using the Session Initiation Protocol, with support for ZRTP encryption
ORBOT
A free software project to provide anonymity on the Internet for users of the Android operating system. It acts as an instance of the Tor network
ORFOX
A Tor Browser for Android, with a few minor modifications to the privacy enhancing features to make them compatible with Firefox for Android
SIGNAL
Free, worldwide, encrypted voice calls for iPhone, and fully compatible with RedPhone for Android - Proprietary code used for voice calls
CHAT SECURE
A free and open source messaging app that features OTR encryption over XMPP (Jabber)
CYANOGENMOD
An open-source operating system for smartphones and tablet computers, based on the Android mobile platform
DATA TRANSPARENCY
IPHONE TRACKER
Maps the information that your iPhone is recording about your movements
COOKIEPEDIA
Provides detailed information all about cookies, the types of data they collect, and the websites that use them.
FLOODWATCH
A Chrome extension that tracks the ads you see as you browse the internet
TERMS OF SERVICE
A project started in 2012 to help fix the “biggest lie on the web”: almost no one really reads the terms of service we agree to all the time
PANOPTICLICK
Analyzes how well your browser and add-ons protect you against online tracking techniques, checks if your system is uniquely configured, and thus identifiable, even if you are using privacy-protective software
BROWSERS
TOR BROWSER
A modified Firefox ESR, pre-configured to protect users' privacy and anonymity on the web, bundled with Tor to allow users to use the Tor anonymity network
ENCRYPTION
TAILS
A live operating system, that you can start on almost any computer from a DVD, USB stick, or SD card, which aims at preserving your privacy and anonymity
GPG
A complete and free implementation of the OpenPGP standard, which allows to encrypt and sign your data and communication
LUKS
Linux Unified Key Setup or LUKS is a disk encryption specification, which specifies a platform-independent standard on-disk format for use in various tools
VERACRYPT
An open-source freeware utility used for on-the-fly encryption. It can create a virtual encrypted disk within a file or encrypt a partition or the entire storage device with pre-boot authentication
ONIONSHARE
An open source tool that lets you securely and anonymously share a file of any size
OTR CHAT
Off-the-Record (OTR) Messaging allows you to have private conversations over instant messaging
POSTEO MAIL
An email provider based in Berlin with a strong focus on sustainability and security
PROTONMAIL
An encrypted-email service which uses client-side encryption to protect email contents and user data before they are sent to ProtonMail servers
DATA VISUALIZATION
OPEN VISUAL TRACEROUTE
An pen source cross-platform Java Visual Traceroute, packet sniffer and Whois. Data is displayed in a 3D or a 2D map component
LIGHTBEAM
Enables you to see the first and third party sites you interact with on the Web, using interactive visualizations, and shows you the relationships between these third parties and the sites you visit
NMAP
A security scanner used to discover hosts and services on a computer network, thus creating a "map" of the network
WIRESHARK
A free and open source packet analyzer, used for network troubleshooting, analysis, software and communications protocol development, and education
OTHERS
JUST DELETE ME
A website and browser extension which helps you delete your accounts from many web services
FAKE IDENTITY GENERATOR
Generates a fake name, address, date of birth, username, password and biography
RUIN MY SEARCH HISTORY
Ruins your Google search history with a single click
GUERRILLA MAIL
Disposable Temporary E-Mail Address
[6] RESEARCH & NETWORK ACTIVISM
ELECTRONIC FRONTIER FOUNDATION
RISEUP
AUSTISTICI
TACTICAL TECH COLLECTIVE
SERVUS.AT
DATA UNION
INSTITUTE OF NETWORK CULTURES
DISRUPTION NETWORK LAB
NETWORKED LABOUR
SHARE LAB
SHARE FOUNDATION
ANNE HELMOND
DYNAMICS OF VIRTUAL WORK
DYNE.ORG
GLOBAL GUERRILLAS
SHARE FOUNDATION
DATA ACTIVE
BITS OF FREEDOM
[7] PROJECTS
SECURITY IN A BOX
MY SHADOW
EXPOSING THE INVISIBLE
FACEBOOK ALGORITHMIC FACTORY
METADATA INVESTIGATION: INSIDE HACKING TEAM
ANNE HELMOND
INSITUTE FOR THE ADVANCEMENT OF POPULAR AUTOMATISMS
DISNOVATION
CITIZEN EX
DATA DEALER
COMMODIFY US
RUIN MY SEARCH HISTORY
HOW MUCH IS YOUR DATA WORTH?
CRITICAL ATLAS OF INTERNET
MAP OF THE INTERNET
[8] TEXTS
Shoshana Zuboff (March 5, 2016). The Secrets of Surveillance Capitalism. Feuilleton. Retrieved from http://www.faz.net/aktuell/feuilleton/debatten/the-digital-debate/shoshana-zuboff-secrets-of-surveillance-capitalism-14103616.html
John Naughton (2015, December 6). ALGORITHM WRITERS NEED A CODE OF CONDUCT. The Guardian. Retrieved from http://bit.ly/2cknps6
Adam D. I. Kramera, Jamie E. Guilloryb, and Jeffrey T. Hancockb, (March 25, 2014). FEXPERIMENTAL EVIDENCE OF MASSIVE-SCALE EMOTIONAL CONTAGION THROUGH SOCIAL NETWORKS. Princeton University. Retrieved from http://www.pnas.org/content/111/24/8788.full
Zoe Corbyn (12 September, 2012). FACEBOOK EXPERIMENTS ON VOTER. University of California, Berkeley - School of Law. Retrieved from http://www.nature.com/news/facebook-experiment-boosts-us-voter-turnout-1.11401
Evgeny Morozov (October 22, 2013). THE REAL PRIVACY PROBLEM. MIT Technology Review. Retrieved from https://www.technologyreview.com/s/520426/the-real-privacy-problem/
Meghan O’Gieblyn (February 09, 2016). As a God Might Be, Three Visions of Technological Progress. Boston Review. Retrieved from https://bostonreview.net/books-ideas/meghan-ogieblyn-god-might-be?utm_content=buffer4e2b3&utm_medium=social&utm_source=twitter.com&utm_campaign=buffer
Lídia Pereira (January 22, 2016). Corporate Social Networking Platforms As Cognitive Factories. Institute of Network Cultures. Retrieved from http://networkcultures.org/longform/2016/01/22/corporate-social-networking-platforms-as-cognitive-factories/
Pamela Samuelson (May 11, 2015). FREEDOM TO TINKER. University of California, Berkeley - School of Law. Retrieved from http://papers.ssrn.com/sol3/papers.cfm?abstract_id=2605195
Neil Lawrence (March 5, 2015 ). Beware the rise of the digital oligarchy . The Guardian. Retrieved from https://www.theguardian.com/media-network/2015/mar/05/digital-oligarchy-algorithms-personal-data
Joanna Geary (April 23, 2012 ). Tracking the trackers: What are cookies? An introduction to web tracking . The Guardian. Retrieved from https://www.theguardian.com/technology/2012/apr/23/cookies-and-web-tracking-intro
Doc Searls (June 7, 2016). What's Our Next Fight? Linux Journal. Retrieved from https://www.linuxjournal.com/content/whats-our-next-fight
Bob Dormon (May 24, 2016). How the Internet works: Submarine fibre, brains in jars, and coaxial cables. Ars Technica. Retrieved from http://arstechnica.co.uk/information-technology/2016/05/how-the-internet-works-submarine-cables-data-centres-last-mile/
Andersen, C.U. y Pold, S., 2011. Interface criticism aesthetics beyond buttons. Aarhus [Denmark]; Oakville, CT: Aarhus University Press ; David Brown Book Co. ISBN 87-7124-239-2.
Barry, A., Arti ce and Design: Art and Technology in Human Experience, Cornell University Press, 2008.
Benjamin, W., La obra de arte en la era de su reproducibilidad técnica, Godot, Barcelona, 2012. Berardi, F., La sublevación, Surplus, Oaxaca, 2014.
Bertelsen, O.W. y Pold, S., 2004. Criticism as an approach to interface aesthetics. Proceedings of the third Nordic conference on Human-computer interaction. ACM Press, pp. 23–32.
Castells, M., La Sociedad Red, Alianza Editorial, Madrid, 2006. Cox, G., Mc Lean, A., Speaking Code, MIT Press, Boston, 2012.
Deleuze, G., Guattari, F., A ousand Plateaus: Capitalism and Schizophrenia, A&C Black, London, 2004.
Feenberg, A., Transformar la Tecnología, Universidad Nacional de Quilmes, Buenos Aires, 2012. Foucault, M., e Archaeology of Knowledge, Paperback, London, 1982.
Fuller, B., Utopia or Oblivion: e Prospects for Humanity, Bantam Books, Nueva York, 1969. Fuller, M. (ed.), 2008. Software studies: A lexicon. Cambridge, Mass.: MIT Press. [Accessed: 26 abril 2016]. ISBN 978-0-262-27334-3.
Fuller, M. y Go ey, A., 2012. Evil Media. Cambridge, Mass: e MIT Press. ISBN 978-0-262-01785-5.
Galloway, A.R., 2012. e interface e ect. Cambridge, UK; Malden, MA: Polity. ISBN 978-0-7456-6252-7.
Grosser, B., 2014. What Do Metrics Want? How Quanti cation Prescribes Social Interaction on Facebook. Computational Culture: a journal of software studies [online], Available at: http://computationalculture.net/article/what-do-metrics-want.
Harrel, F., Phantom Media, MIT Press, Boston, 2014.
Illich, I., La Convivencialidad, Fondo de Cultura Económica, México DF, 2006.
Latour, B., 2005. Reassembling the Social: An Introduction to Actor-Network eory. S.l.: Oxford University Press, USA.
Latour, B., Nunca Fuimos Modernos, Siglo 21 Editores, México DF, 2007.
Liliana, O., 2012. Turing Complete User [en línea]. octubre 2012. [Retrieved: 1 junio 2016]. Available at: http://contemporary-home-computing.org/turing-complete-user/.
Manovich, L., 2002. e Language of New Media. Reprint edition. Cambridge, Mass.: e MIT Press. ISBN 978-0-262-63255-3.
Manovich, L., 2013. Software Takes Command. New York: Continuum Publishing Corporation. ISBN 978-1-62356-745-3.
Marcuse, H., El hombre unidimensional, Ariel, Madrid, 2010. Morozov, E., To Save Everything Click Here:, Paperback, London, 2013.
Padilla, M., 2014. Las interfaces: tres instantáneas [en línea]. 10 junio 2014. Retrieved from: http://pipes.hangar.org/wp-content/uploads/2014/06/interfaces_para_publi- car_margarita_padilla.pdf.
Parikka, J., A Geology of Media, University of Minnesota Press, Minnesota, 2015.
Penny, S., Badia, T., Garcia, M., Parés, R., Balestrini, M., Seebach, S., Perelló, J., et alt., 2015. Protocol para la Investigación Interdisciplinar. [en línea]. [Accessed: 3 junio 2016]. Retrieved from: https://wirkt.hangar.org/index.php/Main_Page.
Shirky, C., Cognitive Surplus, e Penguin Press, New York, 2010.
Terranova, T., Free Labour, Producing Culture for the Digital Economy, London, 2003. Tiqqun, La Hipótesis Cibernética, Acuarela & A. Machado, Madrid, 2015.
Wark, M., Un Manifesto Hacker, Alpha Decay, Barcelona, 2006.
Wiener, N., Cibernética, Barcelona, Tusquets, Barcelona,1985.
[9] ABOUT
RESEARCH
JOANA MOLL
ANDREA NONI
MANAGEMENT & COORDINATION
TERE BADIA
CLARA PIAZUELO
MARTA GRACIA
HANGAR
EUROPEAN CONSORTIUM IMAGIT
Karlsruhe University of Arts and Design – HfG (Karlsruhe, Germany) coordinator of the project.
HANGAR (Barcelona).
Hungarian University of Fine Arts – HUFA (Budapest, Hungary).
Brainz (Prague, Txec Republic).

